Complexity leads to errors. The more complex a system is, the more likely it is to have errors. This is the root of the problem with computer security. The more functionality our systems have, the more difficult it is to defend them.
We now see the affects of complexity in systems with underlying (embedded) computers. An example of this is the Toyota Prius, which is having brake issues due to software related issues. A few years ago it would have been difficult to imagine a software issue affecting the brake system of a car. Now it is a reality, and the future is not looking much better. As more and more complexity is introduced into our devices, errors are more likely to occur.
Another example of this trend is found in our newest computing platform, the smart phone. As a new Droid user I am fascinated by the amount of functionality and computing power available from my phone. I downloaded several applications and started experimenting. After few days of this “download and play” activity, my phone started locking up. It was at that point that I realized that there was a significant amount of risk in what I was doing. Is security an issue on my phone? The short answer, of course it is! Both the iPhone and Android based phones have had security issues. Complexity is the nemesis of security.
Turning our attention to our IT Enterprises, the complexity is immediately apparent. The complexity of a smart phone is dwarfed by the complexity of our IT Enterprises; therefore, the likely hood of a security issue is much higher. In fact, I would go as far as to say that there is a security issue in your IT environment right now (mine too of course).
So what should we do? Panic, and then realize that there is no way to make it completely safe without removing the network cables (and WiFi, USB, CD-RW, floppy drives, etc.)! No, our world is not safe, and that is just the way it is. There is nothing you can do…
 OK, we now see the reality of it, what do we do? In the early days of computer security there was the concept of the hard shell, soft center. Basically this concept was our firewalls form a shell around us, but inside things are not protected. Our connections to the “evil Internet” where all the hackers live are protected by firewalls. We also created DMZ’s (De-Militarized Zones) for our less trusted assets like web servers because these are the systems that the hackers are going to get. Security problem solved, right? Wrong.
OK, we now see the reality of it, what do we do? In the early days of computer security there was the concept of the hard shell, soft center. Basically this concept was our firewalls form a shell around us, but inside things are not protected. Our connections to the “evil Internet” where all the hackers live are protected by firewalls. We also created DMZ’s (De-Militarized Zones) for our less trusted assets like web servers because these are the systems that the hackers are going to get. Security problem solved, right? Wrong.

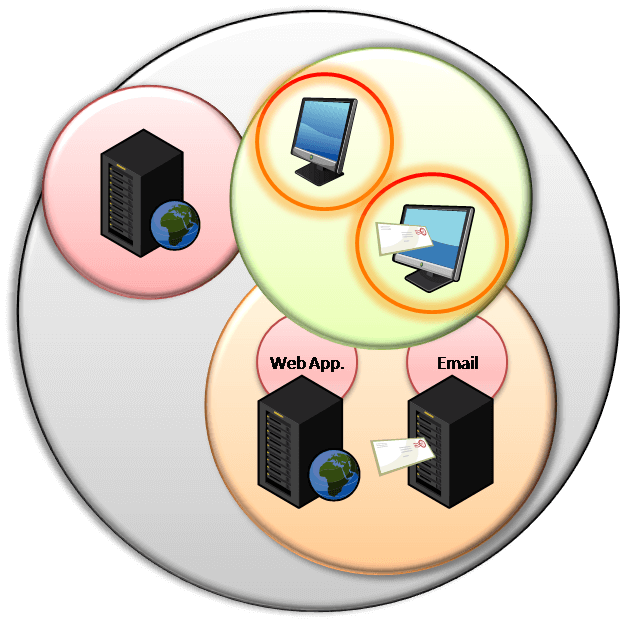
The hard shell, gooey center concept failed long ago. The enemy is no longer at the gate, he is in the castle. Now we need to further divide our systems into zones, and levels, and enclaves. Done? Nope.
We must also limit access to the networks and services within our enterprise. The “ultimate” goal is to limit access to only what the user needs. Consider this, the Sasser worm, which exploited a vulnerability Local Security Authority Subsystem Service (LSASS) in Windows, rapidly speared though several enterprise environments. The interesting aspect of this worm, and others like it, is that it relied on the ability to communicate with other computers on the network. In large Windows workstation environments, the worm quickly spread from workstation to workstation. Usually our workstation environments are connected to a single network (or VLAN) without any limitations. But why would one workstation need to communicate to another workstations? The answer, to spread a virus. If we limited workstation communications with local firewalls or private VLAN, most worms would fail.

The solution is complex and difficult to manage. Security is required at every level; networks, servers, workstations, applications, and our Internet boarders. Perfect security is an unattainable goal. Instead, we must do what we can, within our constraints, to protect what is important. To maximize the return on these efforts, I suggest that we focus on the critical data sets and services, working from the assumption that the enemy is in the castle. Yes, maintain the moat and keep the gate closed, but we must also lock the doors to the treasury and put a couple of guards in the hallway.